Brian Reid – Microsoft MVP and Microsoft Certified Master
-

Blocking onmicrosoft.com Emails in Exchange Online Protection
There is a considerable uptick in emails from the default domain in Microsoft 365 tenants. These emails come from senders @ tenant.onmicrosoft.com and are not your tenant. Microsoft recently announced recipient external sender limits to reduce this, as the default is 10,000 recipients per day, but will get an additional restriction of no more than…
-

Integrating Microsoft 365 SafeLinks and Mimecast Targeted Threat Protection
If your email protection filter is provided by Mimecast, then you might also have enabled Mimecast Targeted Threat Protection (TTP). TTP, like Microsoft Defender for Office SafeLinks will rewrite the URLs in email messages, but unlike SafeLinks will not rewrite or redirect them in Office documents or Teams chat, channel and meetings. Therefore as both…
-

What Is “mx.microsoft”?
mx.microsoft is the new MX delivery domain for Exchange Online. For years now it has been mail.protection.outlook.com, but this domain will not work with the new DNSSEC extensions that Exchange Online will start to support. When you added a new domain (called a vanity domain) to Microsoft 365, it would show you the MX record…
-

Copilot 365 in Teams Meetings – To Transcribe or Not?
In my opinion, one of the clear best features of Microsoft Copilot 365 is the integration with Microsoft Teams Meetings. The ability to ask for meeting notes, unanswered questions, and more is fantastic. But it needs to be (minimally) configured, so this is what you need to check. Some of these settings are per user,…
-
Outlook Reactions – Unsubscribe and Resubscribe
You can “answer” and email in Outlook with a emoji, called a reaction. If you get a reaction in response to a message you will see the reaction in the message, via a notification on the “bell” icon on the top of the Outlook desktop window and in other places, and importantly for this blog…
-

Testing Entra ID Claims and Single Sign-On Enterprise Apps
There is a class of Enterprise App in Entra ID (previously known as Azure Active Directory) that provides SSO (Single Sign-On) for apps outside of Microsoft 365 provided by other vendors. Some of these will be very commonly used apps and others not so. For these apps to sign you into their application with your…
-

Windows LAPS and Granting Roles to Administrative Units
This blog post discusses how to create both a custom admin role for reading the LAPS password and settings stored in Entra ID and then assigning that role so that only device administrators of an Entra ID Administrative Unit can see the local admin password for the subset of devices they are able to manage.…
-

Entra ID Multi-Factor Authentication/Conditional Access and External Federation Implementation
I have a few clients (not many) who have external federation for Entra ID (previously Azure Active Directory) and over the last year or so have been looking into these and integrating them with Entra ID Conditional Access. This has become more of an issue recently with Microsoft’s recently creation of “Microsoft Managed” Conditional Access…
-
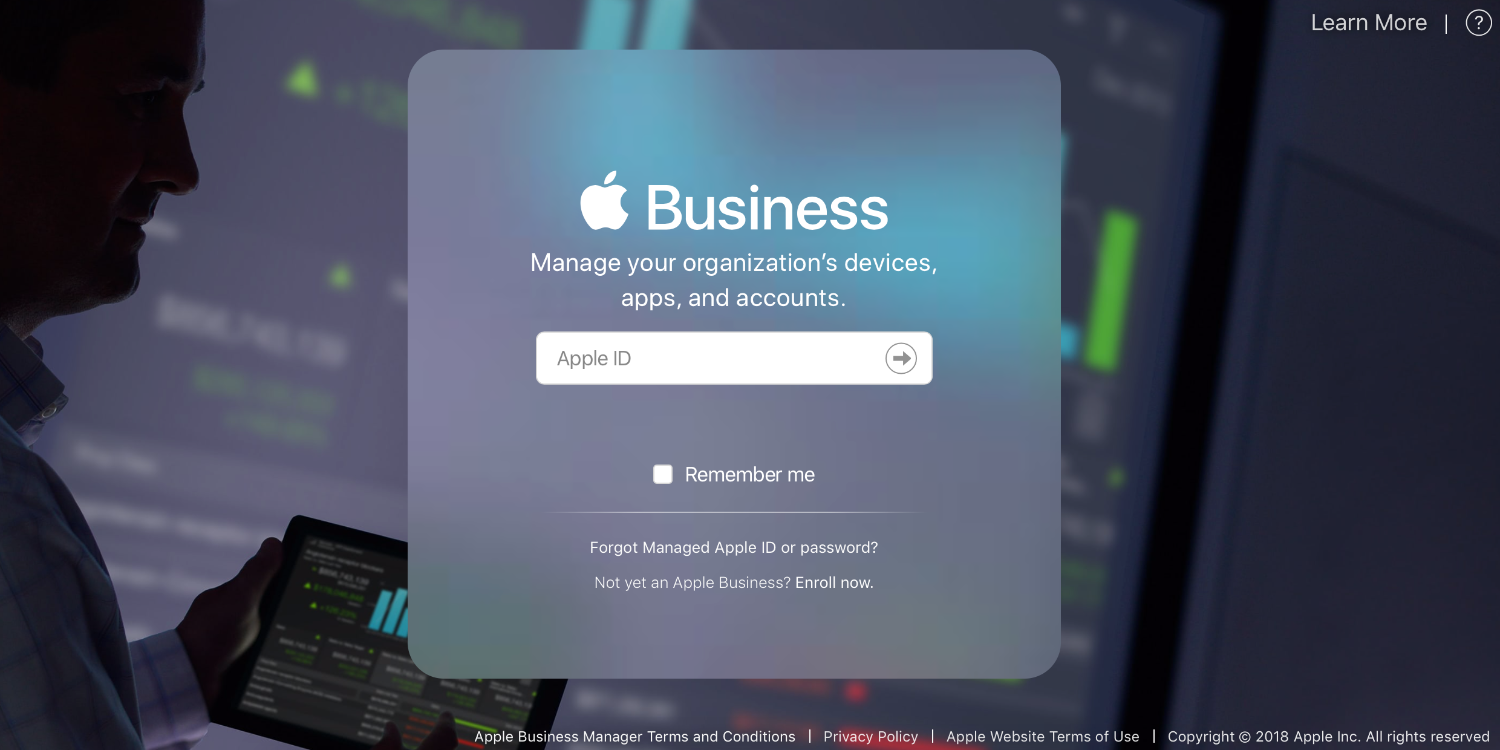
Renewing Apple Tokens in Intune
To sync Apple OS devices to Intune you need a token created by Apple and uploaded to Intune. There are at least 3 seperate tokens that you might use and each of these expires one year after creation and needs renewing before they expire. The three (plus) tokens you need are: Apple MDM Push Certificate…
-

Inviting Google (Gmail) Users To Collaborate In Your Teams Channels
This post is not about inviting Google users to your meetings, where you just send them the meeting invite and all is good. This is about adding the Gmail user as a member of a Team, so they can see the Teams channels, chat and collaborate with files and apps along with everyone else in…
-

Teams v2 Machine Wide Installer
There was a “machine wide installer” for Teams v1 (version 1) that was an .msi file (as opposed to an .exe file) that would install Teams in the “Program Files” folder area (in contrast to the %appdata% folders) so that on machines that had many users (shared devices, hotdesks, multi-user VDI or remote desktops) you…
-

SSL Inspection and Microsoft 365
There are a number of features in Microsoft 365 that do not work if SSL Inspection (also known as TLS Interception) is enabled on your device or network provider. You need to disable the listed URLs that Microsoft provides in its documentation. The problem is there is a lot of disconnected documentation! This blog post…
-

Is That Domain In Entra ID
Occasionally it is useful to know if a domain name is registered with a tenant in Entra ID (previously known as Azure AD). There is a URL to lookup this information as to my knowledge there is not easy portal to query. The URL requires you to add an email address, though the actual user…
-

Enabling BitLocker In Silent Mode Using the Settings Catalog (2023)
There are many blog posts and articles online about the old way to configure silent BitLocker. These used a template that Microsoft added to Intune. Since March 2023 BitLocker has moved (along with lots of other configurations) to using the Settings Catalog. Often the settings are similar and you can take a old blog post…
-

Duplicate rule found: ‘Standard Preset Security Policy’.
If you are editing the Preset Security Policies in Microsoft 365 you might come across the error Duplicate rule found: ‘Standard Preset Security Policy’. There is an easy fix for this – go through the wizard and remove all the users, groups or domains that the rule applies to. This will delete the rule. You…
-
Introduction to Microsoft Graph PowerShell SDK
This short blog post is the 10 minute demo I presented at Microsoft Ignite 2023 in Seattle. It was not recorded, but this was the slide deck that went with it. Graph SDK Additional Content.pptx The full speaking text of the presentation might be added here once the jetlag goes away!
-

Upgrade Teams Room Basic Licences To Teams Room Pro
Teams Room Pro licences come at a licence cost, but provide considerably more features than Teams Room Basic licences (which are free, and limited to 25 rooms per tenant). One of the features available in Teams Room Pro is dual display, and another is the Microsoft Teams Rooms Pro Management portal, but for me the…
-
Bulk Token Retrieval Failed
The Windows Configuration Designer (WCD) application (installed from the Microsoft Store) allows you to bulk convert standalone Windows 10+ clients to Azure AD Joined clients, and if you have Intune auto-enroll enabled then the client will enrol with Intune as well. But there are a number of issues with this application that result in errors…
-

Entra ID and Parental Consent
For organizations that store the data of young adults and children, and in some legal regions, adults who cannot consent to their own legal affairs, you need to record the Age Group for the user, along with any Consent Provided in the case of Minors. There are three categories of Age Group in Entra ID…
-

Migrating from AADConnect Sync to Entra Connect Cloud Sync Correctly
At the time of writing this blog post, the Microsoft guide for doing an AADConnect to Entra ID Cloud Sync migration is lacking quite a lot of detail. It contains the sum of two self referencing documents, one of which is a guide to doing the migration in a lab environment and the other is…
-
SharePoint Org Assets Library Missing Read Permissions for “Everyone Except External Users”
A SharePoint Organization Assets Library allows you to have a central location for Office templates, fonts and images. Various Microsoft 365 apps show this location when in use, for example when creating a new document in Word, the organization templates library can be listed as a source of templates. To create an Organization Assets Library…